General Discussion
Related: Editorials & Other Articles, Issue Forums, Alliance Forums, Region ForumsNSA slide 17: "Show me all the VPN startups"..."So I can decrypt"
Last edited Wed Jul 31, 2013, 08:51 PM - Edit history (1)

H/T to Catherina for finding the image in usable form!
Slide 17 in the Xkeystore presentation starts with the text Show me all the VPN startups.
Now I know most of us here on DU aren't very technical, but as a professional programmer this is the most astounding reveal in the package.
A little background. VPN stands for a Virtual Private Network. A Private Network is a physical network that is not connected to the internet. Some will say that it is a network that sits behind a strong firewall. I would call that a semi private network, but for the purposes of this discussion, that is a good enough definition of private network.
In the networking world a Virtual Private Network is a network connection that uses the internet to route the packets of data (web page bits, documents, etc) but before sending them, encrypts the contents of the packets. This is kinda sorta like using the https protocol in your browser, except VPN encrypts everything sent over the network in a configuration known as peer to peer. Basically your computer in a Starbucks connects to a machine on your home network directly and all the stuff they exchange is encrypted so that nobody can use sniffer tools to look at the packets content, well they can but it won't do any good because it's encrypted.
Now, most likely the software on your machine is written by Cisco and it is talking to a Cisco router on the home network. Cisco is the number one manufacturer of networking gear. Cisco uses good encryption, the kind that even the NSA is not supposed to have the computing power to brute force decrypt.
Now, I saw that slide this morning and DAYUM it smacked me hard! WTF, show me all the VPN startups so I can have them decrypted! Holy fuck Batman!
What this really means is that for any given packet on the internet, the NSA can capture it, and if it is participating in a VPN session, they can decrypt it! This can only mean that the NSA has an edge on encryption stuff. I don't know how, or what edge they have, but the nonchalant use of the decrypt in the slide means they got something to use on it. It could be something in the encryption standard itself, a subtle flaw in all random number generators, or something else, but they seem to be confident they can decrypt any VPN traffic. They don't say Cisco only or something like that, so it makes me wonder about blowfish (about the best open source encryption there is) and other encryption stuff.
I doubt this post will get much attention here, but you can rest assured that to technical types, this is huge. Much that we thought to be secure is now proven otherwise.
I might not be around until this evening to answer questions etc, but I wanted to get this out there, I will follow up tonight on this thread.
leveymg
(36,418 posts)Last edited Wed Jul 31, 2013, 04:03 PM - Edit history (1)
all the commercial OSs, most of the software, and most of the microprocessors and peripherals made in the world, and that if NSA can't grab it and decrypt it as it is sent, the processor somehow alters encryption or creates a copy of every document made and at first opportunity sends it back to the NSA mothership. If NSA is doing this, the others probably are, as well.
You would think that last part would be readily observable, but maybe it's not. Every time my Dell laptop gets a Windows Update, I know there's a 2-way chat. I can also tell you this much, my Chinese-made All-in-One is alive and cycles every now and then, even when it's turned off and not plugged into my computer. But, it only does that when my computer is nearby and I'm on-line. I'm not going to rip it apart to find the Blue Tooth modem, but it's in there, and it's uncanny because the thing seems to have a ghost. But, I digress.
If only a portion of the above scenario is accurate, very little that is created on a computer remains private and escapes the All Seeing One(s). That explains the fact that MS was the first of the NSA providers, and has given NSA a copy of the keys to everything since the first copy of Windows (interesting trade name) was jointly developed and sold OTC.
That's just a hunch. The printer is definitely possessed. ![]()
bunnies
(15,859 posts)Exactly. I keep it next to where my laptop is if Im in the living room. And every now and then it cycles, not plugged in and not connected to the computer. Sometimes I even get the noise... the "doot doot" sound that my computer would make if I were to connect the printer to it. I figured mine was faulty or something. Now Im not so sure. We cant BOTH have haunted printers!
leveymg
(36,418 posts)Did only a quick search. Here: http://www.pcreview.co.uk/forums/hp-printer-switching-itself-t3793290.html
Looks like I'll have to do some googling. The people in that thread were leaving the USB connected, so its not quite the same.
Its that connection sound that bugs me the most because it comes from my computer and the printer isnt attached. So whats connecting? Does it have a stealthy wireless connection that I dont know about?
I know one thing. Im moving this thing away from me. Today. Ghosts I can handle, connecting to the mother-ship, not so much. ![]()
leveymg
(36,418 posts)Occasionally it comes down, and is sighted, as in this footage: ![]()
http://www.metacafe.com/watch/2945804/ufos_sighting_mother_ship_big_disk/
leveymg
(36,418 posts)Way above average production values - even captured the 16mm look to the 1960s "footage."
BlueStreak
(8,377 posts)Who would ever have suspected that?
jberryhill
(62,444 posts)Just change your TV to another channel.

pnwmom
(108,978 posts)Yes. As long as information is kept on computers that are connected in any fashion, no one should expect any privacy anywhere.
Aerows
(39,961 posts)Everyone knows that HP JetDirects were the sole source of all printer possession. Exorcism of HP JetDirects required hands and knees unplugging them and praying that you could telnet back into them to revive their dark hearts.
PowerToThePeople
(9,610 posts)make it look as though the effort to put them in place is worthless. Why spent the effort to set up ipsec vpns or ssh tunnels or whatever to avoid being snooped on if they can snoop anyway?
hootinholler
(26,449 posts)You don't want AirBus to see what's happening. There is still value in encrypting traffic, just not so much if the eyes you are trying to keep away is the NSA.
PowerToThePeople
(9,610 posts)avoiding NSA snooping is something citizens would want to do. if they feel it is impossible, why implement the method?
There was of course no way of knowing whether you were being watched at any given moment. How often, or on what system, the Thought Police plugged in on any individual wire was guesswork. It was even conceivable that they watched everybody all the time. but at any rate they could plug in your wire whenever they wanted to. You have to live - did live, from habit that became instinct - in the assumption that every sound you made was overheard, and, except in darkness, every movement scrutinized.
leveymg
(36,418 posts)dixiegrrrrl
(60,010 posts)I always assumed nothing was private.
A lot of people were accused of being tin foil hatters when they said for years that the gov't is snooping on everything.
hootinholler
(26,449 posts)I mean this capability has the ability to obtain say sales figures for a large corporation at the same time they are transmitted back to the enterprise class systems. The encryption of VPN technology is relied on by literally everyone corporate.
Octafish
(55,745 posts)hootinholler
(26,449 posts)That my friend would be very valuable whilst shopping for bargain corporations to buy, er, invest in.
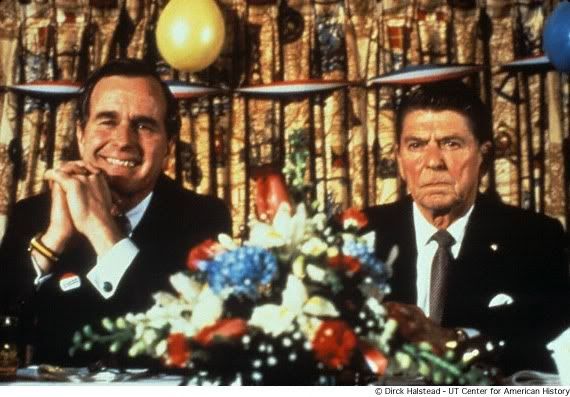
Ronnie doesn't look very happy in that photo. What's the context?
Octafish
(55,745 posts)Just before RNC Nominating Hatefest in 1980.
Guy hadn't even been, eh, inaugurated yet and he looked, eh, befuddled.
Speaking of never knowing what hit the fan, remember that Carlyle investment in Booz Allen?
http://www.democraticunderground.com/discuss/duboard.php?az=view_all&address=103x344031
Lot of fuel under the reactor since then, Hoot. A heck of a lot.
ETA from Richard "Hands in the Cookie Safe" Allen: http://www.hoover.org/publications/hoover-digest/article/7991
LondonReign2
(5,213 posts)steve2470
(37,457 posts)If NSA can hack all VPN and encryption, then no halfway intelligent terrorist is going to use the internet. From what I remember, OBL was using sneakernet completely. We didn't catch him via the internet but (I think) a compromised phone call ?
leveymg
(36,418 posts)Catherina
(35,568 posts)like it's something you do before coffee (see slide in OP)
And in this slide, I'm curious what was redacted. SSL key access?

Bookmarking your thread and looking forward to what else you have to share.
Aerows
(39,961 posts)1. You don't know what you are talking about
2. If you do know what you are talking about, it isn't relevant here.
3. Of course metadata is collected
4. Metadata shouldn't be collected but shut up that's why
5. Metadata isn't collected and even though it is, shut up, that's why.
I'd list the rest, but it's gotten ridiculous.
PowerToThePeople
(9,610 posts)Or just trying to get people to post better arguments against it?
cthulu2016
(10,960 posts)PowerToThePeople
(9,610 posts)Do we have good answers for those concerns?
1. You don't know what you are talking about
Does it matter? NSA should not be spying on citizens.
2. If you do know what you are talking about, it isn't relevant here.
NSA should not be spying on citizens.
3. Of course metadata is collected
NSA should not be spying on citizens.
4. Metadata shouldn't be collected but shut up that's why
NSA should not be spying on citizens.
5. Metadata isn't collected and even though it is, shut up, that's why.
NSA should not be spying on citizens.
Aerows
(39,961 posts)but better arguments would work, too. At least then I wouldn't feel like I need to flush my own head in the toilet bowl due to the stupidity I've heard recently in support of spying on the American people.
I'm sure that's just me.
0rganism
(23,955 posts)Hell, they want our data, and they can probably find a way to get at most of it if they decide they really need to. So why not just take it to the next level, eliminate the fancy-pants snooping middle man, and offer continuous backups ala Carbonite? Then they don't have to decrypt all that annoying network traffic, and they can provide an actual public service at the same time.
spin
(17,493 posts)nadinbrzezinski
(154,021 posts)Yup, we just went down further down the rabbit hole...
WillyT
(72,631 posts)DeSwiss
(27,137 posts)...into Intel and AMD processors, it wouldn't surprise me that they have something likewise with Cisco routers as well.
 - Just a thought......
- Just a thought......
K&R
leveymg
(36,418 posts)Please, see, http://journals.democraticunderground.com/leveymg/317
Posted by leveymg in General Discussion (1/22-2007 thru 12/14/2010)
Tue Oct 16th 2007, 08:18 AM
Part 1. CALEA – Now, Even Starbucks is Required to Spy on You
reusrename
(1,716 posts)This allows the telecoms to claim they do not give direct access to the NSA.
In reality, they do give direct access to the third party and then the third party gives direct access to the NSA.
You know how the NSA actually gets the "content" of a phone call when under warrant?
One thing I wasn't quite aware of back when this was posted, this is all done prior to obtaining any warrants. Those warrants are automatically filed and approved after the information has been collected and viewed.
leveymg
(36,418 posts)the "secret room" at the SF mains switching station, as the EFF case showed. See, https://www.eff.org/nsa-spying/timeline
Maedhros
(10,007 posts)and still claim that the NSA is not collecting content?
nadinbrzezinski
(154,021 posts)Something about keeping you safe...didn't you hear? They stopped attacks, we just can't tell Senators how many...rough paraphrase from the morning
Maedhros
(10,007 posts)I am NOT AFRAID of "terrorism." The probability that I, or one of my loved ones, would be injured or killed from an act of terrorism is so vanishingly small that I simply do not think about it.
STOP TRYING TO PROTECT ME.
MisterP
(23,730 posts)who "will believe I am crazy or believe in the barbed wire that does NOT exist in Jonestown"
so, something like that would go on in their heads
kentuck
(111,098 posts)at the bottom of the slide. What do you think it means?
PowerToThePeople
(9,610 posts)In laymans terms (I am not a network person, but do run my own linux router with dns services and vpn)
It is telling you whether it is a new message, the end of message, or keep "alive" more message is coming.
Rex
(65,616 posts)Or a few 100 years. LOL. Still, this govt needs to quit spying on us and our mundane lives. Whatever happened to fighting the terrorists? Guess we are more important now that some idiot kids blew up bombs in Boston.
Spitfire of ATJ
(32,723 posts)PowerToThePeople
(9,610 posts)did you read all the code?
There have been back doors/trojans found in open source software. We trust that our package maintainers are not going to sell us out.
Spitfire of ATJ
(32,723 posts)Jerry442
(1,265 posts)Imagine a software package that's one whacking big collection of "Mad Libs" with all the keywords that gets the NSA's Juices flowing. Then fill the unused areas of your hard disk with this stuff: documents and emails full of lurid details about evil conspiracies. Swap it between your various computers on your wi-fi and VPNs and email accounts and what have you during slack times.
Make 'em drink from a fire hose, man.
![]()
gvstn
(2,805 posts)But I seem to recall reading about the NSA stance on encryption in the last two weeks. Reading between the lines it seemed to me that they can decrypt anything but not instantly. They wanted backdoors into MS encryption, not because it was impossible to break but that it might take them a few weeks of dedicated processing time to do it alone.
I've always assumed that have far greater processing power than they let on. It wouldn't take them 10,000 years to decrypt a document as some sites seem to suggest but maybe a month for a very sophisticated encrypted document. Similarly, they limit the amount of processing power an individual can legally acquire so they always have a huge edge.
quinnox
(20,600 posts)ProdigalJunkMail
(12,017 posts)in asymmetric key cryptography, how often are private keys generated?
sP
hootinholler
(26,449 posts)I do GIS, not crypto. My guess is once, since they are a private key.
ProdigalJunkMail
(12,017 posts)even simple systems change it once every few days. and with a key that is constantly changing, decryption on a mass scale is for all intents and purposes impossible.
sP
hootinholler
(26,449 posts)But the apropos public key has to be known by whoever is sending you stuff. I've never explored deeply SSL or other stuff, so perhaps you know are fresh keys generated and exchanged at the start of each session? That would be fairly easy to do.
The other thing is that if the NSA has an in somewhere, which the slide seems to imply that they do, changing keys really doesn't matter much.
ProdigalJunkMail
(12,017 posts)very much... why do you feel that you know enough to speak intelligently about it? the public key is not something that is static. it is not like it is something that is just the same key for everyone. it is just half (well, not mathematically) of the key that allows for encrypting the data so that only the person with the other half (the private key) can decrypt the traffic or message or whatever. to suggest that the NSA somehow knows all the public/private key pairs (which are ephemeral in nature) is simply uninformed. the only hope they have is to focus in one very small segments of traffic... and even then the odds are bad and the expenses high.
sP
hootinholler
(26,449 posts)A subtle difference perhaps from very much.
By that I mean I can't tell you exactly how for instance an SSL handshake occurs with what steps. But I have a pretty good functioning handle on how it basically works. I specifically asked you to point out where I have mislead anyone including myself. I am not trying to talk to a technical audience here but I'm very much interested in accuracy.
AFAIK, a given private key will always generate the same public key. Only that private key instance can decode what is encrypted with public key generated using the private key. I really wouldn't call them ephemeral, well at least any more than what is encrypted with them because if you lose the private key the anything encrypted with its public key is lost as well.
I am not suggesting that the NSA has any keys. The slide clearly infers they have the capability to decrypt VPN traffic. How can they accomplish that without knowledge of keys? The only way I can think of is leveraging some fault in random number generation, or some other common underlying technology, that creates a bias. The NSA is the number one employer of mathemagicians. If they couldn't leverage a bias to crack stuff, I don't know who possibly could. Maybe only Cisco equipment is compromised, I don't know the extent of it, but Cisco generated traffic alone would be huge.
What do I have wrong here?
ProdigalJunkMail
(12,017 posts)all this traffic have mislead people is in the basic concept and idea of how encryption functions by pushing the asinine idea that the NSA can just magically decrypt all this stuff because they have an 'in' with the manufacturers of the hardware components that generate the keys used for encrypting not only VPN tunnels (which are ephemeral hence my description) but basic HTTPS traffic in general. there are literally billions of key pairs created and torn down and thrown away EVERY DAY...some of them only lasting for seconds. So...
AES256 allows for 1.1X10^77 permutations. With a computer operating at 10 pFLOPS it would take 3.3X10^56 years to explore all the combinations. That's to break ONE key...
sP
hootinholler
(26,449 posts)At least by brute force.
The notion I am making up claims about their capabilities is bogus. That they are decrypting VPN sessions came from the NSA's own training slide.
So you tell me how they are decrypting it. Or are you claiming the NSA lies to their own analysts about the capabilities available to their disposal?
Harmony Blue
(3,978 posts)as we all are learning little by little as is being revealed.
Aerows
(39,961 posts)because Obama.
That's pretty much the message I've learned here.
Your concerns are noted. They don't matter because Obama.
Your experience at VPN administration is pointless because it isn't Obama heading your department.
ProdigalJunkMail
(12,017 posts)most of them have no idea what they are talking about and spend time propagating garbage that they heard from someone because it sounded good. unfortunately, if you ask them what their background is or to answer a simple question on the technology being discussed you are accused of all but working for the NSA.
oh, well...
sP
Aerows
(39,961 posts)my background on technology. I've never feared a question about that.
ProdigalJunkMail
(12,017 posts)and feel comfortable enough with your background (based on your descriptions of tech and their uses) to know that you know what you are talking about. i have been in the sniffer game for quite some time... and it boggles my mind what some folks will believe is actually possible.
sP
Aerows
(39,961 posts)it's just that there is a lot of horseshit floating around here, and I guess I have an issue with incorrect information being floated as fact.
ProdigalJunkMail
(12,017 posts)i am on your side... there are loads of people here spouting technical quackery and no matter how you try to educate or inform you are shot down. i tried a couple of times a while back... i gave up. now, i just shake my head and see how doctors must feel about bad medical information...
sP
Aerows
(39,961 posts)That's where I'm at. Hey, at least I tried.
hootinholler
(26,449 posts)If so, please elaborate.
ProdigalJunkMail
(12,017 posts)from people who know nothing of the technologies they are trying to talk about. they are simply repeating something that someone somewhere said was true and they believed it because it looked shiny. and if you try to help or god forbid you call them on it, you are suddenly a shill or downright employee of the NSA...
sP
hootinholler
(26,449 posts)KurtNYC
(14,549 posts)they go on to give bad legal advice. Same for "I'm not a doctor..."
Similarly, "Please don't take offense..." is followed by something really offensive.
Go Vols
(5,902 posts)The breakthrough was enormous, says the former official, and soon afterward the agency pulled the shade down tight on the project, even within the intelligence community and Congress. “Only the chairman and vice chairman and the two staff directors of each intelligence committee were told about it,” he says. The reason? “They were thinking that this computing breakthrough was going to give them the ability to crack current public encryption.”
http://www.wired.com/threatlevel/2012/03/ff_nsadatacenter/all/
devils chaplain
(602 posts)Cronus Protagonist
(15,574 posts)Please don't FUCK ME!! I'm using TOR for Christ's sake!!1!
devils chaplain
(602 posts)Cronus Protagonist
(15,574 posts)*thwaaaappp*
![]()
Cronus Protagonist
(15,574 posts)*thwaaaappp*
![]()
winter is coming
(11,785 posts)devils chaplain
(602 posts)Xithras
(16,191 posts)If it's true that the NSA is actually collecting metadata on every connection, then TOR isn't secure either. Even if your connection is encrypted, they can map the connections across every node and do a packet comparison between the traffic coming from your computer, and the traffic passing through each of the exit nodes that your connection may have jumped to. Since they're mapping the entire system, it's relatively trivial to figure out which datastream on which exit node maps to the datastream on your computer. They still have to crack the encryption, but once the onion has been peeled, a TOR network connection is no more secure than any other web connection.
The security of TOR is based on the presumption that your traffic will be shuffled through a series of intermediaries, hiding your identity from the remote computers. The assumption was that nobody could be traced beyond their exit node. If the NSA really has the ability to record all connections across the Internet, then they can also track traffic BETWEEN the nodes between the nodes and TOR end users. That breaks the whole TOR privacy model.
winter is coming
(11,785 posts)GiaGiovanni
(1,247 posts)Could you explain to a technically challenged person what this all means?
hootinholler
(26,449 posts)Um, first, I'm not an encryption expert. Second, this is the explanation for the technically challenged, or at least I thought it was, but I'm often mistaken.
If you let me know what bits are troubling you, I'll be happy to try a better explanation.
GiaGiovanni
(1,247 posts)Does every computer have it? OR only those separate from the internet? How do you get encryption on your computer?
hootinholler
(26,449 posts)The most common is built into your browser. When you connect to a site using https instead of http there is some indicator like a golden lock that you connection is secure. The browser knows how to encrypt and decrypt the stuff it is sending and receiving.
There are companion programs or modules that allow you send and receive encrypted email that work with thunderbird or outlook. Now if you use web based email, then I don't know what encryption is available.
Then there is the kind I talk about in this thread when you want a secure connection to another computer (or network) like when you work at home and have sensitive information to be sent back. That is when things like VPN come into play. To get that you have to install software. Most likely it will be from Cisco, who makes a vast majority of networking hardware.
There are other options as well. You can encrypt all or part of your hard drive (which I think some form is built into windows, but I wouldn't trust it) or just some files. For that, you would have to install some software.
So sometimes it's built into something you are using and other times you have to install it on your machine.
I can certainly understand your confusion.
GiaGiovanni
(1,247 posts)What you're op is saying then is that NSA can break Cisco encryption software?
(Pardon me for being clueless.)
hootinholler
(26,449 posts)It appears that they can break any encryption in use by VPN software. Now Cisco is the biggest provider of that but not the only one.
GiaGiovanni
(1,247 posts)Except to keep files hidden from "nobodies"?
hootinholler
(26,449 posts)The capabilities of the NSA are extraordinary.
GiaGiovanni
(1,247 posts)Thanks. So their capabilities are way above what most people in the industry thought they were.
hootinholler
(26,449 posts)I'm still wondering if they can crack BlowFish (which is an open source encryption system that is among the best there is.)
I suspect they are taking advantage of some hardware flaw that is very common. Maybe even introduced into chipsets by request.
GiaGiovanni
(1,247 posts)Sorry. ![]()
You think they have a flaw built into a chip?
hootinholler
(26,449 posts)Among many.
![]()
We will likely never know for sure.
GiaGiovanni
(1,247 posts)I appreciate the fact that you tried to explain what you know. I do know a bit more than I did before, so consider that a victory. ![]()
Uncle Joe
(58,364 posts)Thanks for the thread, hootinholler.
okieinpain
(9,397 posts)The gov can and is doing this. Lol, with everything being digital its really easy to save and store data. To me the biggest hurdle to data collection is the cost of storage.
Well guess what folks storage is dirt cheap, a simple joe can easily put together a six core cpu pc with 8 terabytes of high speed disk space for under $2000 without breaking a sweat.
So just imagine what old uncle sam can buy with a 100 billion dollars. Lol, dont get upset about it just think of it as stimulating the economy.
GiaGiovanni
(1,247 posts)and TIA
hootinholler
(26,449 posts)GiaGiovanni
(1,247 posts)I've only heard the bad press.
hootinholler
(26,449 posts)They facilitate research into a lot of things. Some are build a better bomb (bad press) others are figure out how to make computers talk to each other.
GiaGiovanni
(1,247 posts)actually TIA from the beginning?
hootinholler
(26,449 posts)Mainly because the goal of the internet was the internet: A universal way to allow computers to talk to each other. That's not to say that there wasn't military advantage to pursuing the research.
GiaGiovanni
(1,247 posts)I know that universities were in the forefront because it was an easier way to share research.
steve2470
(37,457 posts)Rosa Luxemburg
(28,627 posts)I'm sure if the Nsa can do that the Chinese can.
hootinholler
(26,449 posts)I'll have to give that one some thought. I'll grant there is a possibility there.
struggle4progress
(118,290 posts)a vendor's sales presentation
Recursion
(56,582 posts)Interesting, if troubling, to see it implemented. But, yeah, if you can really keep all traffic you should be able to do the key management backwards.