General Discussion
Related: Editorials & Other Articles, Issue Forums, Alliance Forums, Region ForumsGCHQ(NSA) tap fibre-optic cables for secret access to world's communications
Last edited Fri Jun 21, 2013, 08:43 PM - Edit history (1)
GCHQ taps fibre-optic cables for secret access to world's communications
Exclusive: British spy agency collects and stores vast quantities of global email messages, Facebook posts, internet histories and calls, and shares them with NSA, latest documents from Edward Snowden reveal
Ewen MacAskill, Julian Borger, Nick Hopkins, Nick Davies and James Ball
guardian.co.uk, Friday 21 June 2013 17.23 BST

Secret document detailing GCHQ's ambition to 'master the internet'
Britain's spy agency GCHQ has secretly gained access to the network of cables which carry the world's phone calls and internet traffic and has started to process vast streams of sensitive personal information which it is sharing with its American partner, the National Security Agency (NSA).
The sheer scale of the agency's ambition is reflected in the titles of its two principal components: Mastering the Internet and Global Telecoms Exploitation, aimed at scooping up as much online and telephone traffic as possible. This is all being carried out without any form of public acknowledgement or debate.
One key innovation has been GCHQ's ability to tap into and store huge volumes of data drawn from fibre-optic cables for up to 30 days so that it can be sifted and analysed. That operation, codenamed Tempora, has been running for some 18 months.
...
This includes recordings of phone calls, the content of email messages, entries on Facebook and the history of any internet user's access to websites – all of which is deemed legal, even though the warrant system was supposed to limit interception to a specified range of targets.
...
Read the rest here: http://www.guardian.co.uk/uk/2013/jun/21/gchq-cables-secret-world-communications-nsa
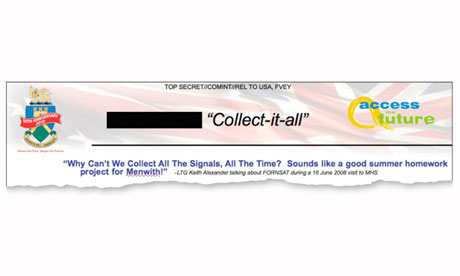
Document quoting Lt Gen Keith Alexander, head of the NSA, during a visit to Britain
TIP OF THE ICEBERG. If your not doing anything wrong, your have nothing to fear. It was true in 1930 Germany and it's true now.
"It's not just a US problem. The UK has a huge dog in this fight. They (GCHQ) are worse than the US." - Edward Snowden
BlueCheese
(2,522 posts)Collect-it-all, Mastering the Internet, and Global Telecoms Exploitation.
I guess the problem with only snooping on foreigners is that we're all foreigners to someone else.
Catherina
(35,568 posts)That Congress needs to ask these liars is "what percentage of the world's intercepted communications aren't shared between you and your 4 partners?"
Anything else just opens the questioning to more word salads.
bobduca
(1,763 posts)where bad = domestic
jsr
(7,712 posts)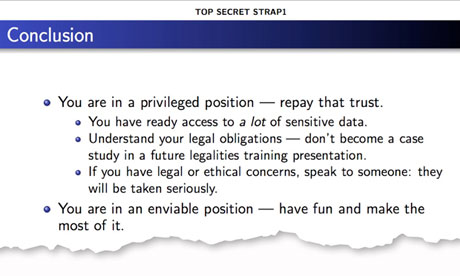
Catherina
(35,568 posts)Kinne described the contents of the calls as "personal, private things with Americans who are not in any way, shape or form associated with anything to do with terrorism."
She said US military officers, American journalists and American aid workers were routinely intercepted and "collected on" as they called their offices or homes in the United States.
...
Faulk says he and others in his section of the NSA facility at Fort Gordon routinely shared salacious or tantalizing phone calls that had been intercepted, alerting office mates to certain time codes of "cuts" that were available on each operator's computer.
"Hey, check this out," Faulk says he would be told, "there's good phone sex or there's some pillow talk, pull up this call, it's really funny, go check it out. It would be some colonel making pillow talk and we would say, 'Wow, this was crazy'," Faulk told ABC News.
...
http://abcnews.go.com/Blotter/exclusive-inside-account-us-eavesdropping-americans/story?id=5987804#.UcEehpxCklq
Monkie
(1,301 posts)looks like this is going to be part of quite a few training presentations in future ![]()
BlueCheese
(2,522 posts)... that this is just a scheme to embarrass Obama dreamt up by Republicans or "haters".
This is a real issue of huge importance.
premium
(3,731 posts)the detractors will be here soon to tell us all just how wrong we are and why we need to ignore it.
intaglio
(8,170 posts)The accurate claim is that these old stories are only now being pushed by the M$M to damage the current President. These stories have, prior to this time, never received such sustained and neurotic coverage. This drive to damage the President at any cost are being assisted by three classes of left wingers.
The first are the inattentive chicken littles who seem never to have looked at any story about such monitoring before now; this despite the fact that this monitoring has been an open secret for years. These are also the ones who seem to have no real idea about how the internet, or cell phone systems, work.
The second are the outrage junkies, who need their fix of moral superiority. They will explain at length how no other President has ever been as deceptive, unconstitutional or controlling as the current one, and it matters not if that President is a Democrat or a Republican.
The third and most damaging class are the knee-jerk revolutionaries; these do not desire a President who undermines what they see as the inevitable apocalypse of total corporate control, or Randian Social Darwinism or Plutonomy or whatever else they are now calling it this week. Their aims are:
a) to be proven right in their dire prophecies;
b) to see a collapse of the centre left; and
c) to see the socialist revolution the believe is "inevitable".
To this end they will stir up as much trouble as possible to damage both the President and the Democratic party
nadinbrzezinski
(154,021 posts)but hey, we are all racists (spied upon) now.
![]()
Catherina
(35,568 posts)Speak for yourself. I am NOT a racist. I am a self-hating Black who *hates* my President, not because of his rightwing policies, not because his administration is crawling with the same Bush Republicans we chased out in 2008, not because of drones, or wars, or destabilizing other countries, no, just because he's Black. ![]()
Fucking wow. In what cesspool did someone come up with the idea of throwing charges of racism at the same people who elected and supported him?
nadinbrzezinski
(154,021 posts)so there...
(What is sad is that both of us are making fun of this canard, since it is real pathetic)
Catherina
(35,568 posts)And yeah..., it's real pathetic. I'm not sure how much lower it can go.
nadinbrzezinski
(154,021 posts)I would not ask that question if I were you. The digging will continue until morale improves...
Catherina
(35,568 posts)Not that I want to look. I just want to know if they've found something more effective than the old "Look! Ron Paul" bullshit. I got called a teabagger last week! Can you imagine that lol? OMG. Too funny. Too desperate. Too transparent.
nadinbrzezinski
(154,021 posts)Is.....bbbbbaaaaaacccckkk!!!!!
Catherina
(35,568 posts)Screw that.
If your not doing anything wrong, your have nothing to fear. It was true in 1930 Germany and it's true now.
That which we do not resist we will be forced to accept.
nadinbrzezinski
(154,021 posts)Now it's an active case. This means people will shut up, since it is an active case.
Catherina
(35,568 posts)nadinbrzezinski
(154,021 posts)Those folks probably want to dispense with the trial.
An open trial? Yup, sure, sure.
intaglio
(8,170 posts)Prior to this time revelations about these programs has never stopped them. All that will happen is that th Republicans will act outraged and insist "something must be done" ie elect Republicans. The few genuinely outraged Democratic Congress persons will attempt to put into a law something that stops this or de-funds it and fail. If the controversy doesn't fade before Nov 2014 (unlikely, public attention being very short lived) it will lead to no real change in control of Congress because the things that really matter (womens rights, Gay rights, corporate responsibility) will take second place to this storm in a teacup.
nadinbrzezinski
(154,021 posts)Have you heard, outside f Paul, any Rs screaming?
Me neither. They won't touch this. It's bipartisan.
snooper2
(30,151 posts)This is the dumbing down of journalism that is really pathetic. It's just a series of tubes right?
I suggest reading up on DWDM before you think there's is just a strand or two of fiber and they got all me data ma!
LOL
nadinbrzezinski
(154,021 posts)or was that possible just because it was done during the Bush years?
snooper2
(30,151 posts)I don't think you really grasp the amount of fiber optic cable in the World, how traffic routes, technologies like DWDM or how carriers interconnect for Voice and/or Data traffic...
Have you ever even held a piece of fiber in your hand?
This picture mean anything to you?
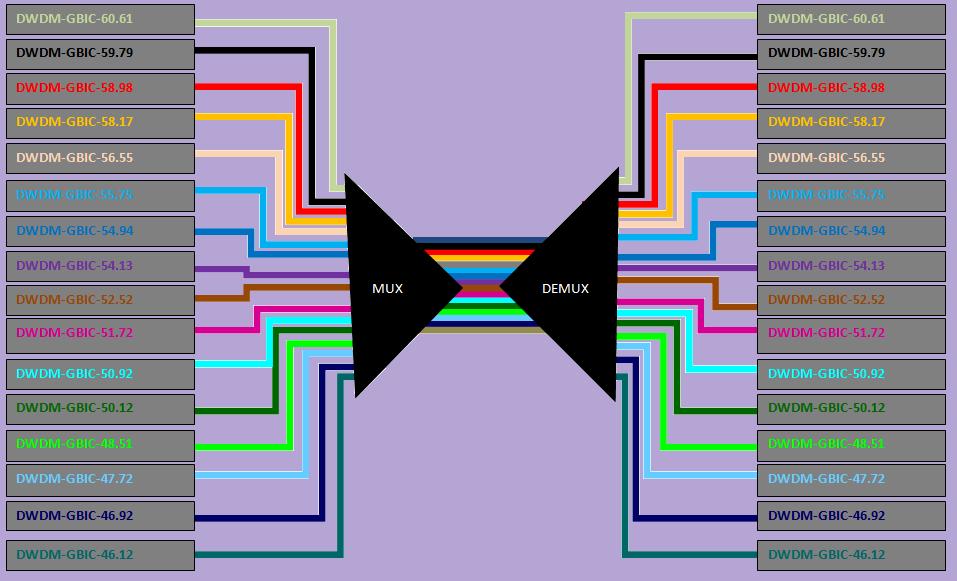
This make sense?
The Zettabyte Era is upon us. Cisco research indicates that the total volume of worldwide IP traffic is doubling every two years. By 2012, the world's IP networks will transport 44 exabytes of traffic - equivalent to 522 exabytes per year, or a little over half a Zettabyte - each month. This growth will be driven not just by an expanding user base, but by the emergence of a new generation of complex, highly personalized, bandwidth-intensive media applications.
These trends are compelling service providers to rethink their approaches to core network architectures. How can network operators achieve the scalability to support the enormous bandwidth demands of the coming years? How can they extend intelligence throughout the network to deliver innovative services with superior quality? How can they move beyond the static optical networking model of the past to an environment that supports dynamic, end-to-end provisioning of any service, anywhere, any time? One architecture can make this vision a reality today: IP over dense wavelength-division multiplexing (IPoDWDM).
With the convergence of IP intelligence and DWDM transport technology in Cisco® IPoDWDM solutions, service providers around the globe are realizing:
• Significant capital savings by eliminating layers of transponders between IP and optical network layers
• Lower total cost of ownership through a simpler architecture with fewer network elements, remote manageability, and unprecedented wavelength flexibility
• Next-generation provisioning and protection capabilities through the integration of IP- and optical-layer intelligence
Now, Cisco is extending the value of its IPoDWDM portfolio even further with a suite of powerful new features that enhance scalability and efficiency, and fulfill the promise of infinitely flexible, end-to-end optical provisioning.

nadinbrzezinski
(154,021 posts)have a good day. Last answer you will get from me on this subject.
snooper2
(30,151 posts)Question-
What is the average number of hops for a domestic voice call?
I'm going to a forum in a couple months to talk about carrier interconnections, HD Voice, getting away from PSTN tandems- Maybe I can get a pass for you! Did you know Verizon has over 10,000 DMS switches which over the next 10 years they'll have to decommission? You know what EOL and EOS mean?
randome
(34,845 posts)[hr]
[font color="blue"][center]You should never stop having childhood dreams.[/center][/font]
[hr]
nadinbrzezinski
(154,021 posts)is not exactly the true capabilities of these agencies? We are not exactly talking of OFF THE SHELF COMPONENTS here.
I made an exception to try to make a point that I think you are missing.
FYY, these NOT OFF THE SHELF COMPONENTS ARE CLASSIFIED... and so are their capabilities.
They did not go to Fry's...
They were snooping into TELEX and other communications back in the Seventies using Telsat, which is not what you would consider doable back then by people on the civilian side of the house. Yet they were... using the Five Eyes. It was called ECHELON.
You also assume that the rubes here have no knowledge of any of this shit... some of us DO...
So thank you for trying to explain CIVILIAN capabilities that use off the shelf components and could not do what they are doing... alas Bimmey and others have referred to this gear as NOT OFF THE SHELF...
I think the person who does not wish to learn anything is you, and I get it... this is troubling and can challenge the self. See nothing, hear nothing and say nothing is a good self protecting mechanism...
Have a good day... don't bother trying to correct me... I know I am an idiot on this according to you, we get it. And a few other things... so that is that.
snooper2
(30,151 posts)to their central location?
Over the public Internet?
nadinbrzezinski
(154,021 posts)And experts who have testified to this...are also idiots.
Here is the position you find yourself in, either you are telling us the true capabilities of these programs, in which case you are breaking security...(for god sakes make it so). Or you are clueless and a civilian, while the whistle blowers have told the truth.notice did not use the singular here.
Which is it?
You might think we are awed by pretty pictures of off the shelf components, that you could conceivably get at Fry's, or worst case a large data company...but you might want to check back, we are not in awe from text book material.
So are you breaking security? Or are you working on the civilian side of the house, and simply can't believe this?
I am willing to bet on number two.
If I told you that the FBI has white noise generators I am sure you would also tell me that is not true. In that case I trust my lying eyes.
I get it...this is disconcerting, troubling and all that. So you have a choice...seriously...listen to those who have been trying to warn you, with all that this implies...or continue to sleep. I suspect you will take number two. Just be careful of security bear, it can turn on you in an instant, even when you are a good citizen.
Have an excellent day.
Oh and reading bellow...civilian. You are not working with the gear these people are working with...which once again, is not off the shelf. It's nice to establish that.
Monkie
(1,301 posts)or barely related jargon, that has so little relevance, instead of asking meaningless questions of people that you know dont have the technical expertise to answer them why not educate them as to what is relevant, and do it graciously, its easier to laugh though?
for example, you laugh about the ATT leak, but the person leaking that information knew what they were talking about, that was not a janitor that leaked the existence of the room with the equipment to tap the lines was it?
let me ask you a question or two,
these soft switches you speak of, they do or dont have remote access capabilities?
they do or do not still have "hard" passwords that give the manufacturer or their tech support people access for diagnostic purposes?
you can or cant update these machines, in part or in total, via remote access?
i think these are more interesting questions than, how many hops does a call make, which is completely immaterial.
ProdigalJunkMail
(12,017 posts)you have fought the good fight and tried to shed a little light on the chicken-littles that inhabit the InterWebs. it is amazing that people with no technical knowledge whatsoever will come in and just scream and scream about something they have no understanding of, and then when someone tries to explain it (or at least the complexities) they are shouted down as being uninformed and a 'civilian' and just trying to confuse them with technical matters that somehow the magicians at the NSA can get around with a wave of a single strand of single-mode fibre.
one question for the person who seems to think civilians can't understand all this whizzy tech that the gov't uses : Who built the internet? Not the original one that is little more than a faint shadow of what is there today... the modern one. Who builds all that tech that allows us to sniff the lines? Hint : it ain't the gov't...
sP
dkf
(37,305 posts)Monkie
(1,301 posts)any nerd could make that up as they go along, it is mostly a bunch of jargons thrown together.
snooper does seem to know something about this subject, but its a shame they dont actually say anything meaningful or actually teach us something new instead of just mocking. and in the end it is just a footnote to the FISA docs that were leaked.
temmer
(358 posts)now I'd like a quote from the Guardian article which is plain wrong in your opinion und why it's wrong in your opinion.
Monkie
(1,301 posts)at every exchange and every provider.
i pay extra for my internet, because my provider takes my government to court every time they attempt to limit privacy or spy on its users, my provider has this listening equipment installed, it went right up to the high court to fight it, and was open about it with its customers from the start.
why are american providers not open about it, why did they not take it to the supreme court, why is it all a secret in the US.
nadinbrzezinski
(154,021 posts)do not need to be told what could trouble them...this is the attitude of the US government. And it will only get worst.
Monkie
(1,301 posts)if you dont phrase the questions right, the forked tongues can work their "magic".
so many of the so called journalists are part of the problem, i remember helen thomas, now there was a woman who knew how to question authority, of course a women, most of us men are weak when it comes down to it.
nadinbrzezinski
(154,021 posts)To the horror of my editor.
I raised the Dulles overheard conversation with the former speaker.she was not happy.
snooper2
(30,151 posts)ridiculous-
You know how many fiber routes we have coming out of one central office?
If you want to tap a voice call, there are LI (lawful intercept) functionality built into class 5 voice switches (TDM or VoIP). Since I happen to be one of the folks who approves who has access, at least within our network, trust me no "NSA analyst" can get in-
Shit, I can't even get into the CLI with my VPN client at home, have to be on our internal network. That's why we contract with a third party for CALEA support. We send them the data for a valid warrant and They in turn send it to LEA.
Also, there are limitations to the number of subscribers you can have a tap on at any moment in time. It's not like I can shit extra 10G interfaces on the servers that are handling production traffic and "duplicate" everything back to the federal government. That would be absolutely ridiculous and the sheer volume of data would make it useless. Plus networks are designed to duplicate the load they have just so we can send everything to the feds. I don't think you understand network topologies. You think the NSA went and put a mirror port on every router in the country? And before you say (it's in the Core), what about traffic that stays on the edge routers and has a single hop back out to another endpoint?
Who is your provider and what is this court case you are talking about?
I expect that on some oceanic routes the NSA are tapping information. Like, why is there a sudden increase in data and "traffic" from Sudan to BFE Montana? I also suspect that some foreign entities inside the U.S. are being tapped. I also suspect they are smart enough to do things like, oh, ICMP traffic, lets just throw that away ![]()
Monkie
(1,301 posts)who makes your switches?
what provider are you talking about?
you just told me you do contract out for CALEA support, same as every other provider out there, but at the same time you are making jokes that these taps are not there.
so there are limitations on the number that can be tapped at one time, how many exactly?
you say at the same time that you cant "shit extra 10G interfaces and duplicate" as that you say "plus the networks ARE designed to duplicate the load so we can send everything to the feds"
what has icmp traffic have to do with any of this in any meaningful way? you saying it cant be dropped/ignored or what are you saying?
shall we start with that and then we can go into more detail on with the rest of your little story?
snooper2
(30,151 posts)to support and provide data to LEA,
VS-
The getting all the data in the world, all calls, all SMTP, everything-
jeez- No, not going to tell you who I work for-
You can do a little google search for the top two SoftSwitch manufactures and that will give you a hint. One starts with a B and the other starts with a S ![]()
Monkie
(1,301 posts)and yes there is a difference between lawful intercepts and "getting all the data in the world"
but you and i both know that there is a hell of a lot more going on here than just your garden variety lawful intercepts by "regular" LEA
and bringing up SMTP has nothing to do with any of this, you know that if you do deep packet inspection, or have a switch, any piece of network equipment, it can be configured however you like, to drop whatever protocol or part of the layer you want, you can slice it and dice it, thats what the stuff is designed for in the first place.
im not completely stupid, ok? ![]()
Jarla
(156 posts)starting at post 27?
We're discussing the technology that might be involved.
Monkie
(1,301 posts)im going to be afk for a little while but then i will have a look at that part of the discussion.
i would say that i think it is a mistake to be looking at the technology involved, i think it is mainly irrelevant, what is important is the documentation, and the lies being told, there seems to be a clear chronology of leak-lie-leak as proof-new lie etc, that is easy to follow, it is the laws that need changing, and the lies of lawmakers that can make that happen, and getting bogged down in technical details wont help with that?
nadinbrzezinski
(154,021 posts)Jarla
(156 posts)Some people are using others' ignorance of how this technology works as a weapon against them. "You don't know enough about this stuff to know what you're talking about." (Though this isn't the case at all in my current discussion with Catherina)
Monkie
(1,301 posts)its just a tactic, because "they" have no answer to the real documentation, or the chronology of the lies, if you want to beat them, use the weapons you do have, make sure your chronology is tight, leak-lie-leak-lie, because this is the real gift that snowden and greenwald gave us, this is clear as day, you have clappers lies, you have muellers lies, you have the hearings, you have obama's lies even.you have the documentation, and the law, if you line that up correctly you will be unbeatable, and then the technology used to achieve the surveillance is immaterial, there are people for that.
i will have a quick look at what you asked me to look at, but i hope you understand why its immaterial, you can break all the equipment in the world with the law.
Jarla
(156 posts)temmer
(358 posts)snooper2
(30,151 posts)from every company in the World,...
Latency be damned!
Customer- How come I call from my office in Jersey to our DC location and I get so much echo?
Me- Oh, that's normal
Customer- What do you mean normal?
Me- Oh, we route every single packet through San Francisco
Customer- What! Why are you doing that?
Me- It's a secret, but it adds 180ms of round trip delay so you'll have to deal with it
Customer- WTF! ![]()
Monkie
(1,301 posts)see my other reply to you.
DesMoinesDem
(1,569 posts)No one is suggesting that there is just a strand or two of fiber optic cable. That's just your strawman used to attack the article, and it is pathetic.
Access to the future 1 Document quoting Lt Gen Keith Alexander, head of the NSA, during a visit to Britain
Each of the cables carries data at a rate of 10 gigabits per second, so the tapped cables had the capacity, in theory, to deliver more than 21 petabytes a day – equivalent to sending all the information in all the books in the British Library 192 times every 24 hours.
And the scale of the programme is constantly increasing as more cables are tapped and GCHQ data storage facilities in the UK and abroad are expanded with the aim of processing terabits (thousands of gigabits) of data at a time.
usGovOwesUs3Trillion
(2,022 posts)Or that they intended that these docs be released to trick people into thinking they have capabilities that they don't really have, some kinda reverse psychology thing?
I'm sorry, but I'm not following what your are getting at... can you please elaborate what you think specifically these docs are saying, please.
Please, quote the documents in your response.
Thank you.
temmer
(358 posts)unfortunately a disappointment for those who like to paint Greenwald and Snowden as isolated nuts. Greenwald has obviously the full backing of his bosses, and the issue will not go away.
Catherina
(35,568 posts)The issue not only won't go away but is growing larger. This is more than just about US citizens being spied upon, this is about spying on your allies and *hoovering* trade and intellectual property from all over the world. In these challenging economic times, that's not going over very well.
I keep wondering when they're going to put a gag order on the Guardian lol.
marions ghost
(19,841 posts)---
Catherina
(35,568 posts)
Slide about NSA analysts using data coming from both Prism and from the fiber-optic cables
Jarla
(156 posts)Since the GCHQ can store and analyze any of the data that the NSA isn't allowed to look at and then share it with the NSA. Brilliant!!
FarCenter
(19,429 posts)Since WW II, international telephone and telegraph traffic has been intercepted from international cables.
Nothing new.
Businesses and governments already know to encrypt all traffic transiting the US, UK, Canada, Australia and New Zealand. No one depends on the carriers transmission lines being secure, either from governments or various other organizations.
The trickier bit is placing taps on undersea fiber optic cables using specially modified submarines. This has been done on cables that do not land in one of those five countries.
Catherina
(35,568 posts)How PRISM actually works: 15-20 AT&T fiber optic hubs have NSA-installed light splitters just upstream of major tech companies, copying ALL INTERNET DATA that passes through to those companies onto the NSA network.
[hr]
According to security expert Steve Gibson and court testimony by an AT&T technician from 2006, the NSA gets major tech companies' data, probably without their permission or knowledge, by forking off fiber optic light signals (as a prism would) just upstream of where all of the 9 companies in the slides purchase their bandwidth. The technician talks about the installation of a secret room by the NSA in AT&T's San Francisco facility at 611 Folsom Street, San Francisco.
This way, NSA can snoop on nearly all data going into major tech companies without actually connecting to their servers.
... The NSA has said they had direct access to these companies' servers. Well, and that's the funny thing, the thing I noticed when I realized what was going on is that "server" is the only word anyone knows. The word that we should have been using is "router." ...
routers concentrate data. Somewhere, and the NSA knows exactly where it is, Google is buying their bandwidth. And there are routers upstream of Google whose purpose it is to take the disparate packets all coming into Google and route them down fiber-optic lines which finally make the transit into Google's data center. It is unnecessary to have access to the datacenter if you are tapping the fiber-optic line going into and out of the datacenter.
...
So what we have is we have this system called PRISM. We have this bunch of companies that are absolutely sure that they have never agreed to blanket eavesdropping/wiretapping with the NSA. And I believe them. If the NSA had reason to specifically require data that is specific to a given case, we already know they go to a court, they get a warrant, and under a bond of secrecy they're able to get the data that the company has, if any, and the company is bound not to say it.... Essentially what we have is
wiretapping of these companies.
https://www.grc.com/sn/sn-408.pdf
Podcast by Steve Gibson on SecurityNow: http://aolradio.podcast.aol.com/sn/sn0408.mp3
AT&T one-page summary of the splitting process: https://www.eff.org/files/filenode/att/presskit/ATT_onepager.pdf
Legal testimony from 2006 by AT&T technician explaining the splitter and NSA secret rooms at AT&T, which came to light in a 2006 case of the Electronic Frontier Foundation: http://cryptome.org/klein-decl.htm
Photo of secret room in the San Fran facility:

2006 WIRED coverage of the case: "AT&T Sued Over NSA Eavesdropping" January 31, 2006 http://www.wired.com/science/discoveries/news/2006/01/70126
Most testimony is about 1 security room that was busted because of a problem with excess condensation. NSA Whistleblowers stated that there were approximately 20 of these secret NSA rooms throughout the US back when they were working for NSA.
[hr]
Paraphrasing from a friend here: These companies can deny all day long that the NSA has access to their servers, and they'd be telling the truth. And they can parade around their disclosure reports showing that the NSA/FBI asked for data only a few times last year, and have a long discussion of how diligently they argued against those disclosures, while completely ignoring the fact that the splitters had already given away a lot of the information, meaning that the NSA didn't need to ask for it, they already had it.
Jarla
(156 posts)And I was told that Steve Gibson is incorrect about his understanding of how PRISM works.
http://www.democraticunderground.com/10023030035
Catherina
(35,568 posts)so that tells you something right there.
People who try to explain this using their limited understanding of how products at Radio Shack work have a different agenda more in line with the government's CYA than transparency. Finally, we are getting some tip-of-the-iceberg transparency here.
The ACLU doesn't know what they're talking about.
The experts don't know what they're talking about.
The whistelblowers don't know what they're talking about.
The ATT technician doesn't know what they're talking about.
NSA's slides don't really mean what they wrote.
GCHQ's slides don't really mean what they wrote.
Oh yeah, and Glenn Greenwald and everyone else daring to bring things up and jeopardizing Obama's legacy are racist.
I'm sorry I didn't see your thread when you posted it.
Jarla
(156 posts)seems to be saying that PRISM works differently from what Steve Gibson is suggesting.
http://bigstory.ap.org/article/secret-prism-success-even-bigger-data-seizure
Though who knows if the AP reporters know what they're talking about?
Catherina
(35,568 posts)but I know hair-splitting when I see it. The bottom line is that they're *hoovering* the world's communications and that they prefer we get tangled up in weeds than focus on the real issue.
The companies that the splitters to capture part of the signal passing down the cables have been booming.
Privatized intelligence like Booz Allen and Hamilton are making an obscene profit for the same people who lied the world into several wars.
And they want to hair-split lol. Just tell them no thank you.
Jarla
(156 posts)And I honestly don't think dfk was either. I'm just trying to sort out what each of these various programs actually does.
Catherina
(35,568 posts)If you were, you'd be on my ignore list as a waste of time lol. And I think highly of dfk. I apologize for writing that in a way that gave you that impression. Omg, no.
Monkie
(1,301 posts)you have different sets of slides, and different programs, thats where some of the confusion comes from.
now looking at what catharina posted..
you have the data from the eff, which i think one can assume is trustworthy, which is META, it is analysis not pure tech, or pure dump/leak.
the cryptome site is well known, but for raw leaks only, that is the "original wikileaks" it is just raw dumps of data, you still need to understand it.
then you have wired magazine, well respected in tech circles, they probably have the best explanations for a non-tech or semi-tech-literate person, but some of the guys there are quite close to the 3 letter agencies, they often speak to "anonymous sources", and you have no idea how much of what they say is the whole truth. but again, they are well respected in tech/nerd circles for their coverage.
then there is gibson, you have to understand something about the whole tech/net/software world, it is so complex, no one person can begin to understand it all.
gibson used to be very relevant, was well known for developing some software, 10+ years ago, but this was software mainly for working with hard disks, and some basic security stuff if i remember right, what i do remember is he started/had these newsletter/podcasts about security issues, some of it good, some of it soso, but my recollection was that it was often simplified for those with the most basic understanding of computers, so in the eyes of those with more experience in a "given subset of expertise" he sometimes missed part of the point, or was flat our wrong, but this was more to do with how he simplified things for the non-technical user.
so without even going into any detail i hope you see how complex this is and how someone can say that gibson is wrong for example.
it is just a hugely complex subject, there are so many different layers to the technical side of it, and there are few people that can actually give you a full picture, and all those people will have their own biases as well.
this is why i say, focus on the released data and the lies, and nothing more, because that is already a lot to take in and for you to line up all your ducks. but if you do, this is where you have the obvious proof to show anyone, technical or non-technical, where the problems are. and then it does not matter what the technical story is of someone trying to throw you of course, because there is no machine that can explain the lies.
I'd never heard of Gibson before, but I read through the transcript of Gibson's podcast, and his explanation sounded very sensible. But I've since seen other explanations of how PRISM works and what it does.
Gibson's explanation seems to be based mostly on his own analysis and speculation. He could very well be wrong, but I don't get the impression that he's deliberately trying to mislead his audience. (I could be completely wrong about that; like I said, I'd never heard of him before so I don't know his history.)
I do suspect, though, that some other "sources" are being deliberately obtuse and confusing in the explanations that they are giving reporters. Because the explanations I've read in various articles don't all match.
Which is interesting. Because we now have a pretty clear idea of what MAINWAY is. It's the database that stores the metadata for phone calls. But PRISM is actually still quite mysterious.
But I do agree with you that there's a lot to work with just with the leaks and the lies.
i would agree with you about gibson, in no way has he ever given the impression that hes deliberately misleading people, and he does have a long history of doing newsetters/podcasts. but he does tend to give his own view on things.
and of course there are sources trying to confuse us.
this is a $80 billion a year industry, some people are getting very rich in this system, there is a lot at stake.
but that is the whole beauty of this really, we have snowden, we have a primary source with documents that nobody has disputed, this is unheard of, completely unheard of, and i think that is why "everyone" is ignoring them as much as possible.
but greenwald is staying very focused on these documents and his knowledge as a lawyer. the ACLU seems very focused too.
Coyotl
(15,262 posts)L. Coyote Nov-09-07
Are ALL COMMUNICATIONS routed overseas to circumvent US law and the Constitution?
http://www.democraticunderground.com/discuss/duboard.php?az=view_all&address=389x2245762
Is that Bush's and the Telecom's HUGE crime hidden and covered-up ...................
jsr
(7,712 posts)
Menwith Hill
Coyotl
(15,262 posts)Fiber-optic cables make this all too easy.
muriel_volestrangler
(101,297 posts)It's been doing its best to ignore all the revelations. Now they've seen this can't be swept under the carpet. 2nd most viewed story on their site now: http://www.bbc.co.uk/news/uk-23004080
Monkie
(1,301 posts)their coverage has been a sad joke, and even now you can see how poorly they attempt to frame this, its embarrassing.
DRoseDARs
(6,810 posts)eom
BenzoDia
(1,010 posts)Life Long Dem
(8,582 posts)More legal activity to come.
Jarla
(156 posts)usGovOwesUs3Trillion
(2,022 posts)Guess that kills that theory, eh?
Arctic Dave
(13,812 posts)The collection of device location through triangulation and vehicle tracking through onstar.
The truth will be worse then we all realize.
Catherina
(35,568 posts)I want to see more about *Blarney* right now because the two programs are used together. If, we have investigations, and Congress doesn't understand that this is about a lot more than just Prism, we're doomed.
Blarney seems to me to be the fiber optic tapping part of it. So dear Congress, don't ask things like "Can Prism do this" or "Do you do that with Prism collected information" but ask them instead "Do any of your programs"

I agree that the truth will be worse then we all realize, that's why it's classified Top Secret/Special Intelligence/No Foreign Eyes/Comint
NoForn means not even our sisters in crime the Brits.
Jarla
(156 posts)From the WaPo
Catherina
(35,568 posts)This whole thing is about economics and keeping little people in line to protect the 1%'s capital. That's where the lines are drawn and they know it.
Thank you Jarla
Monkie
(1,301 posts)The term Blarney has thus come to mean 'the ability to influence and coax with fair words and soft speech without giving offense'
maybe this has something to do with them tapping into the blackberries/voip/skype and/or text messaging services on the internet.
Catherina
(35,568 posts)
Monkie
(1,301 posts)i do think that the leaks from within FISA are the ones where clapper will need some more rhetoric to save himself, because that really showed up the lies. the tapping of fiber optics while explosive is for me not as damaging as showing the lie that is the oversight and the warrant process within FISA. proof of the tapping is nice, but that feels like 20-30 year old news i think for anyone that follows tech/privacy/tradecraft, it was always rumoured. i think what has changed there is the sheer quantity they can process and store.
Tierra_y_Libertad
(50,414 posts)KoKo
(84,711 posts)Catherina
(35,568 posts)I just hope it's to really report and not to divert. I hope they're not foolish enough to try to divert because their credentials have been slipping. Either way, that's good news. Now where's the US press? ![]()
- - -
(video report) ... One such warrant seen by the Guardian shows that they do not contain detailed legal rulings or explanation. Instead, the one-paragraph order, signed by a FISA court judge in 2010, declares that the procedures submitted by the attorney general on behalf of the NSA are consistent with US law and the fourth amendment. (end clip)
GWEN IFILL, NEWSHOUR: Thank you, Glenn. Now for analysis is Rep. Elmer Fudd, chairman of the House Un-Intelligence Activities Committee. Congressman Fudd?
FUDD: Thank you, Gwen. The surveillance was approved by an act of Congress in 2009 and has had judicial review, so it's perfectly legal. And it has stopped terrorist attacks, lots and lots of them.
GWEN: How do you know?
FUDD: Because Congress, or at least my Committee, or at least me and a few others, have been regularly briefed.
GWEN: When? How often?
FUDD: I can't really say. We're sworn to secrecy. I'd like to keep my first-born child, if I could. But the FISA court did sign off on it
GWEN: They seem to have rubber-stamped it.
FUDD: Can't get more efficient than that, yes sirree.
GWEN: And now, it's pledge week, when PBS turns our programming over to local stations so they can keep programs like this on the air.
http://discussion.guardian.co.uk/comment-permalink/24480665
usGovOwesUs3Trillion
(2,022 posts)/sarcasm
I suppose there will be some who will still be in denial, but these NEW documented revelations will leave a mark, as well they should, hopefully that mark will lead to substantial change as well.
Thanks for sharing ![]()
Catherina
(35,568 posts)before the June 2008 FISA vote. But now I'm a [s]racist[/s] self-hating Black and all vile manners sorts of things.
The mark is international. US and UK papers aren't reporting it but it's there. Other countries are demanding, demanding more information and none too pleased with the word salads the US and UK expect people to believe.
I dunno. One morning I woke up and there I was, staring at the underside of a big bus in 2008, simply for being unhappy about his FISA vote. I'm getting to like the underside of this bus. The company is the best. ![]()
usGovOwesUs3Trillion
(2,022 posts)Whenever I see posts here asking DUers their opinion on liberal positions we still win BIG, just the same as we did in 2001, and this issue wins just the same (really this issue, privacy, is bipartisan, especially for Americans) only the vocal minority disagree in the most dissipicable, vile, robotic way possible (some are obviously on the corporate payroll, as real people have memories, and heart).
Though I am a little taken aback that the racist smears are allowed to stand here (though I prefer transparency over censorship) but they are revealing, and say so much more about the accusers than the accused.
It is going to be hard for the totalitarians to sweep this under the rug though, so they are gonna have to make a choice, change or finally admit what they are, and what they have transformed America into; a totalitarian state.
Love ya ![]()
Catherina
(35,568 posts)If I had the time, I'd just hand them a larger brush lol and then a shovel. Never ever interrupt your enemy when he's self-destructing. The minute he starts, run to your nearest Sears Roebuck and offer a catalog more of tools. Here, take your pick! Sledgehammer? Chainsaw? It's on me lol. And if you're from Canada, you get a 10% discount.
![]()
usGovOwesUs3Trillion
(2,022 posts)lol