Welcome to DU!
The truly grassroots left-of-center political community where regular people, not algorithms, drive the discussions and set the standards.
Join the community:
Create a free account
Support DU (and get rid of ads!):
Become a Star Member
Latest Breaking News
Editorials & Other Articles
General Discussion
The DU Lounge
All Forums
Issue Forums
Culture Forums
Alliance Forums
Region Forums
Support Forums
Help & Search
General Discussion
In reply to the discussion: Erik Prince linked to undercover scheme to infiltrate Democratic party organizations [View all]Kid Berwyn
(18,610 posts)29. History from Alfred McCoy and Christopher Simpson
Surveillance Blowback: The Making of the U.S. Surveillance State, 1898-2020
For well over a century, what might be called ‘surveillance blowback’ from America’s wars has ensured the creation of an ever more massive and omnipresent internal security and surveillance apparatus. Its future (though not ours) looks bright indeed.
By Alfred W. McCoy
July 15, 2013 by TomDispatch.com
The American surveillance state is now an omnipresent reality, but its deep history is little known and its future little grasped. Edward Snowden’s leaked documents reveal that, in a post-9/11 state of war, the National Security Agency (NSA) was able to create a surveillance system that could secretly monitor the private communications of almost every American in the name of fighting foreign terrorists. The technology used is state of the art; the impulse, it turns out, is nothing new. For well over a century, what might be called “surveillance blowback” from America’s wars has ensured the creation of an ever more massive and omnipresent internal security and surveillance apparatus. Its future (though not ours) looks bright indeed.
In 1898, Washington occupied the Philippines and in the years that followed pacified its rebellious people, in part by fashioning the world’s first full-scale ‘surveillance state’ in a colonial land. The illiberal lessons learned there then migrated homeward, providing the basis for constructing America’s earliest internal security and surveillance apparatus during World War I. A half-century later, as protests mounted during the Vietnam War, the FBI, building on the foundations of that old security structure, launched large-scale illegal counterintelligence operations to harass antiwar activists, while President Richard Nixon’s White House created its own surveillance apparatus to target its domestic enemies.
In the aftermath of those wars, however, reformers pushed back against secret surveillance. Republican privacy advocates abolished much of President Woodrow Wilson’s security apparatus during the 1920s, and Democratic liberals in Congress created the FISA courts in the 1970s in an attempt to prevent any recurrence of President Nixon’s illegal domestic wiretapping.
Today, as Washington withdraws troops from the Greater Middle East, a sophisticated intelligence apparatus built for the pacification of Afghanistan and Iraq has come home to help create a twenty-first century surveillance state of unprecedented scope. But the past pattern that once checked the rise of a US surveillance state seems to be breaking down.
Despite talk about ending the war on terror one day, President Obama has left the historic pattern of partisan reforms far behind. In what has become a permanent state of ‘wartime’ at home, the Obama administration is building upon the surveillance systems created in the Bush years to maintain US global dominion in peace or war through a strategic, ever-widening edge in information control. The White House shows no sign - nor does Congress - of cutting back on construction of a powerful, global Panopticon that can surveil domestic dissidents, track terrorists, manipulate allied nations, monitor rival powers, counter hostile cyber strikes, launch preemptive cyberattacks, and protect domestic communications.
Writing for TomDispatch four years ago during Obama’s first months in office, I suggested that the War on Terror has “proven remarkably effective in building a technological template that could be just a few tweaks away from creating a domestic surveillance state - with omnipresent cameras, deep data-mining, nano-second biometric identification, and drone aircraft patrolling ‘the homeland.’"
That prediction has become our present reality - and with stunning speed. Americans now live under the Argus-eyed gaze of a digital surveillance state, while increasing numbers of surveillance drones fill American skies. In addition, the NSA’s net now reaches far beyond our borders, sweeping up the personal messages of many millions of people worldwide and penetrating the confidential official communications of at least 30 allied nations. The past has indeed proven prologue. The future is now.
CONTINUED...
https://www.opendemocracy.net/en/surveillance-blowback-making-of-us-surveillance-state-1898-2020/
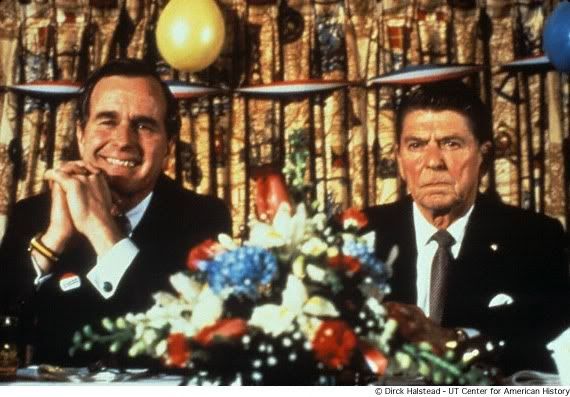
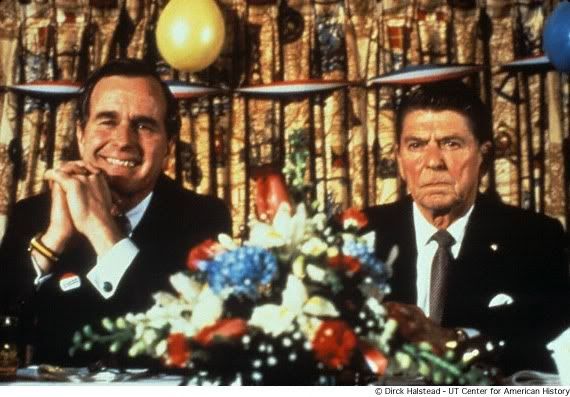
Doesn’t matter if Reagan was a high functioning vegetable, Poppy Bush helped speed the process.
George Bush Takes Charge: The Uses of ‘Counter-Terrorism’
By Christopher Simpson
Covert Action Quarterly 58
A paper trail of declassified documents from the Reagan‑Bush era yields valuable information on how counter‑terrorism provided a powerful mechanism for solidifying Bush's power base and launching a broad range of national security initiatives.
During the Reagan years, George Bush used "crisis management" and "counter‑terrorism" as vehicles for running key parts of the clandestine side of the US government.
Bush proved especially adept at plausible denial. Some measure of his skill in avoiding responsibility can be taken from the fact that even after the Iran‑Contra affair blew the Reagan administration apart, Bush went on to become the "foreign policy president," while CIA Director William Casey, by then conveniently dead, took most of the blame for a number of covert foreign policy debacles that Bush had set in motion.
The trail of National Security Decision Directives (NSDDS) left by the Reagan administration begins to tell the story. True, much remains classified, and still more was never committed to paper in the first place. Even so, the main picture is clear: [font size="5"][font color="green"]As vice president, George Bush was at the center of secret wars, political murders, and America's convoluted oil politics in the Middle East.[/font color][/font size]
SNIP...
Reagan and the NSC also used NSDDs to settle conflicts among security agencies over bureaucratic turf and lines of command. It is through that prism that we see the first glimmers of Vice President Bush's role in clandestine operations during the 1980s.
SNIP...
NSDD 159. MANAGEMENT OF U.S. COVERT OPERATIONS, (TOP SECRET/VEIL‑SENSITIVE), JAN. 18,1985
The Reagan administration's commitment to significantly expand covert operations had been clear since before the 1980 election. How such operations were actually to be managed from day to day, however, was considerably less certain. The management problem became particularly knotty owing to legal requirements to notify congressional intelligence oversight committees of covert operations, on the one hand, and the tacitly accepted presidential mandate to deceive those same committees concerning sensitive operations such as the Contra war in Nicaragua, on the other.
The solution attempted in NSDD 159 was to establish a small coordinating committee headed by Vice President George Bush through which all information concerning US covert operations was to be funneled. The order also established a category of top secret information known as Veil, to be used exclusively for managing records pertaining to covert operations.
The system was designed to keep circulation of written records to an absolute minimum while at the same time ensuring that the vice president retained the ability to coordinate US covert operations with the administration's overt diplomacy and propaganda.
Only eight copies of NSDD 159 were created. The existence of the vice president's committee was itself highly classified. The directive became public as a result of the criminal prosecutions of Oliver North, John Poindexter, and others involved in the Iran‑Contra affair, hence the designation "Exhibit A" running up the left side of the document.
CONTINUED...
CovertAction Quarterly no 58 Fall 1996 pp31-40.
Piratized intel services for privatized profiteering.
For well over a century, what might be called ‘surveillance blowback’ from America’s wars has ensured the creation of an ever more massive and omnipresent internal security and surveillance apparatus. Its future (though not ours) looks bright indeed.
By Alfred W. McCoy
July 15, 2013 by TomDispatch.com
The American surveillance state is now an omnipresent reality, but its deep history is little known and its future little grasped. Edward Snowden’s leaked documents reveal that, in a post-9/11 state of war, the National Security Agency (NSA) was able to create a surveillance system that could secretly monitor the private communications of almost every American in the name of fighting foreign terrorists. The technology used is state of the art; the impulse, it turns out, is nothing new. For well over a century, what might be called “surveillance blowback” from America’s wars has ensured the creation of an ever more massive and omnipresent internal security and surveillance apparatus. Its future (though not ours) looks bright indeed.
In 1898, Washington occupied the Philippines and in the years that followed pacified its rebellious people, in part by fashioning the world’s first full-scale ‘surveillance state’ in a colonial land. The illiberal lessons learned there then migrated homeward, providing the basis for constructing America’s earliest internal security and surveillance apparatus during World War I. A half-century later, as protests mounted during the Vietnam War, the FBI, building on the foundations of that old security structure, launched large-scale illegal counterintelligence operations to harass antiwar activists, while President Richard Nixon’s White House created its own surveillance apparatus to target its domestic enemies.
In the aftermath of those wars, however, reformers pushed back against secret surveillance. Republican privacy advocates abolished much of President Woodrow Wilson’s security apparatus during the 1920s, and Democratic liberals in Congress created the FISA courts in the 1970s in an attempt to prevent any recurrence of President Nixon’s illegal domestic wiretapping.
Today, as Washington withdraws troops from the Greater Middle East, a sophisticated intelligence apparatus built for the pacification of Afghanistan and Iraq has come home to help create a twenty-first century surveillance state of unprecedented scope. But the past pattern that once checked the rise of a US surveillance state seems to be breaking down.
Despite talk about ending the war on terror one day, President Obama has left the historic pattern of partisan reforms far behind. In what has become a permanent state of ‘wartime’ at home, the Obama administration is building upon the surveillance systems created in the Bush years to maintain US global dominion in peace or war through a strategic, ever-widening edge in information control. The White House shows no sign - nor does Congress - of cutting back on construction of a powerful, global Panopticon that can surveil domestic dissidents, track terrorists, manipulate allied nations, monitor rival powers, counter hostile cyber strikes, launch preemptive cyberattacks, and protect domestic communications.
Writing for TomDispatch four years ago during Obama’s first months in office, I suggested that the War on Terror has “proven remarkably effective in building a technological template that could be just a few tweaks away from creating a domestic surveillance state - with omnipresent cameras, deep data-mining, nano-second biometric identification, and drone aircraft patrolling ‘the homeland.’"
That prediction has become our present reality - and with stunning speed. Americans now live under the Argus-eyed gaze of a digital surveillance state, while increasing numbers of surveillance drones fill American skies. In addition, the NSA’s net now reaches far beyond our borders, sweeping up the personal messages of many millions of people worldwide and penetrating the confidential official communications of at least 30 allied nations. The past has indeed proven prologue. The future is now.
CONTINUED...
https://www.opendemocracy.net/en/surveillance-blowback-making-of-us-surveillance-state-1898-2020/
Doesn’t matter if Reagan was a high functioning vegetable, Poppy Bush helped speed the process.
George Bush Takes Charge: The Uses of ‘Counter-Terrorism’
By Christopher Simpson
Covert Action Quarterly 58
A paper trail of declassified documents from the Reagan‑Bush era yields valuable information on how counter‑terrorism provided a powerful mechanism for solidifying Bush's power base and launching a broad range of national security initiatives.
During the Reagan years, George Bush used "crisis management" and "counter‑terrorism" as vehicles for running key parts of the clandestine side of the US government.
Bush proved especially adept at plausible denial. Some measure of his skill in avoiding responsibility can be taken from the fact that even after the Iran‑Contra affair blew the Reagan administration apart, Bush went on to become the "foreign policy president," while CIA Director William Casey, by then conveniently dead, took most of the blame for a number of covert foreign policy debacles that Bush had set in motion.
The trail of National Security Decision Directives (NSDDS) left by the Reagan administration begins to tell the story. True, much remains classified, and still more was never committed to paper in the first place. Even so, the main picture is clear: [font size="5"][font color="green"]As vice president, George Bush was at the center of secret wars, political murders, and America's convoluted oil politics in the Middle East.[/font color][/font size]
SNIP...
Reagan and the NSC also used NSDDs to settle conflicts among security agencies over bureaucratic turf and lines of command. It is through that prism that we see the first glimmers of Vice President Bush's role in clandestine operations during the 1980s.
SNIP...
NSDD 159. MANAGEMENT OF U.S. COVERT OPERATIONS, (TOP SECRET/VEIL‑SENSITIVE), JAN. 18,1985
The Reagan administration's commitment to significantly expand covert operations had been clear since before the 1980 election. How such operations were actually to be managed from day to day, however, was considerably less certain. The management problem became particularly knotty owing to legal requirements to notify congressional intelligence oversight committees of covert operations, on the one hand, and the tacitly accepted presidential mandate to deceive those same committees concerning sensitive operations such as the Contra war in Nicaragua, on the other.
The solution attempted in NSDD 159 was to establish a small coordinating committee headed by Vice President George Bush through which all information concerning US covert operations was to be funneled. The order also established a category of top secret information known as Veil, to be used exclusively for managing records pertaining to covert operations.
The system was designed to keep circulation of written records to an absolute minimum while at the same time ensuring that the vice president retained the ability to coordinate US covert operations with the administration's overt diplomacy and propaganda.
Only eight copies of NSDD 159 were created. The existence of the vice president's committee was itself highly classified. The directive became public as a result of the criminal prosecutions of Oliver North, John Poindexter, and others involved in the Iran‑Contra affair, hence the designation "Exhibit A" running up the left side of the document.
CONTINUED...
CovertAction Quarterly no 58 Fall 1996 pp31-40.
Piratized intel services for privatized profiteering.
Edit history
Please sign in to view edit histories.
Recommendations
0 members have recommended this reply (displayed in chronological order):
36 replies
 = new reply since forum marked as read
Highlight:
NoneDon't highlight anything
5 newestHighlight 5 most recent replies
RecommendedHighlight replies with 5 or more recommendations
= new reply since forum marked as read
Highlight:
NoneDon't highlight anything
5 newestHighlight 5 most recent replies
RecommendedHighlight replies with 5 or more recommendations
Erik Prince linked to undercover scheme to infiltrate Democratic party organizations [View all]
Kid Berwyn
Jun 2021
OP
Which reminds me, we still haven't gotten to the bottom of the Trump Tower/Spectrum Health/Alfa Bank
tanyev
Jun 2021
#5
This shouldn't just be about Prince, though; it should piss us off that Brits like Seddon show up
ancianita
Jun 2021
#13
This is what happens when the punishment is light regarding Projectile Vomitus.
chowder66
Jun 2021
#15
While his wife lay dying of cancer, thought it would be a good idea to impregnate the nanny.
keithbvadu2
Jun 2021
#16
As serious as this is, my first reaction was "what a ridiculous farce". It almost reads
niyad
Jun 2021
#19
Oh we can infiltrate right wing groups now? Awesome. I'm sending 5000 people into them right now
ZonkerHarris
Jun 2021
#30